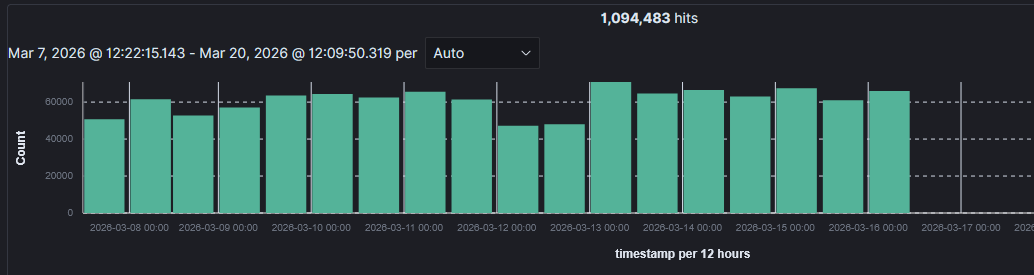
502,000 Reasons to Audit Your Attack Surface: Detecting and Responding to a Sustained Brute Force Campaign
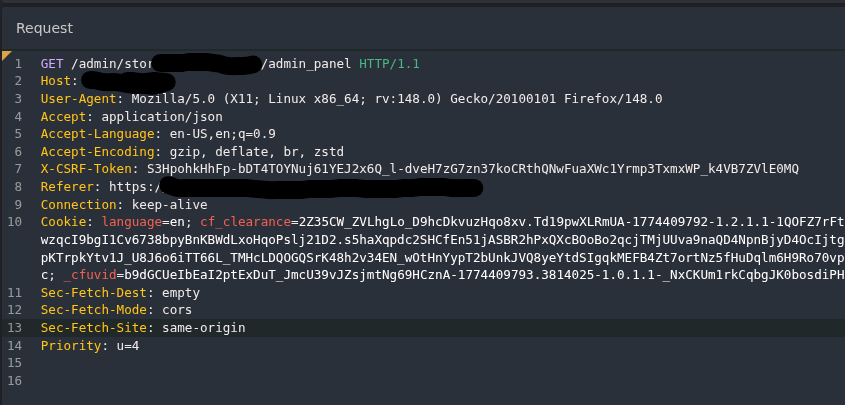
One of the quieter benefits of continuous security monitoring is that it catches things you weren’t looking for. You set up detections for one set of threats, and it finds something else entirely. Something that should have been addressed long ago.